
When I was eight, the Sycamore Canyon Fire forced our family to evacuate. We would pack, watch the fire with our neighbors, then pack some more. My brother and I had tote bags for our things, and we argued over which toys and stuffed animals to bring. My father packed his suits and ties. I asked why he needed all those boring clothes, if our house was burning down.
He said, "The house might burn, but I still have to work, and I need my clothes to do that.” (We were fortunate, and our house did not burn.)
This was my fathers on the fly risk assessment to protect his family. He recognized that he could not show up in court, he ran a small law practice, in his chinos and t-shirt even if his clothes and his house burned down. This experience led to our entire family conducting a risk assessment and creating a plan for all sorts of potential disasters.
Have a plan was his motto. Does your business have a plan? What if the unthinkable happens what will you do? The process of going through a risk assessment seems daunting, but it really isn’t. You do not have to think of all the things the first time, more will come to you as time passes and your plans will become more robust. We didn’t have a mud slide plan for years.
Build Your Risk Assessment
Just like my father proactively addressed potential family risks, your business requires a dynamic approach to risk management. A formal Risk Assessment document is essential, not as a static record, but as a living tool for tracking and monitoring potential threats.
Gathering key representatives from all business functions for regular reviews is crucial. Initially, semi-annual reviews may suffice, but as your comfort and familiarity with the process grow, you can adjust the cadence.
Download Your Risk Assessment Template
Your Assets
The first step is identifying your crucial assets – the tools of your trade. Consider these categories:
- Technology: Software, hardware, systems
- Business Tools: Equipment, machinery, intellectual property
- Buildings: Physical structures, facilities
- Clients: Key relationships, customer base
- Employees: Personnel, skills, expertise
- Finances: Capital, revenue streams, investments
- Vendors: Suppliers, partners, dependencies
Documenting these vital assets forms the foundation for identifying potential risks.

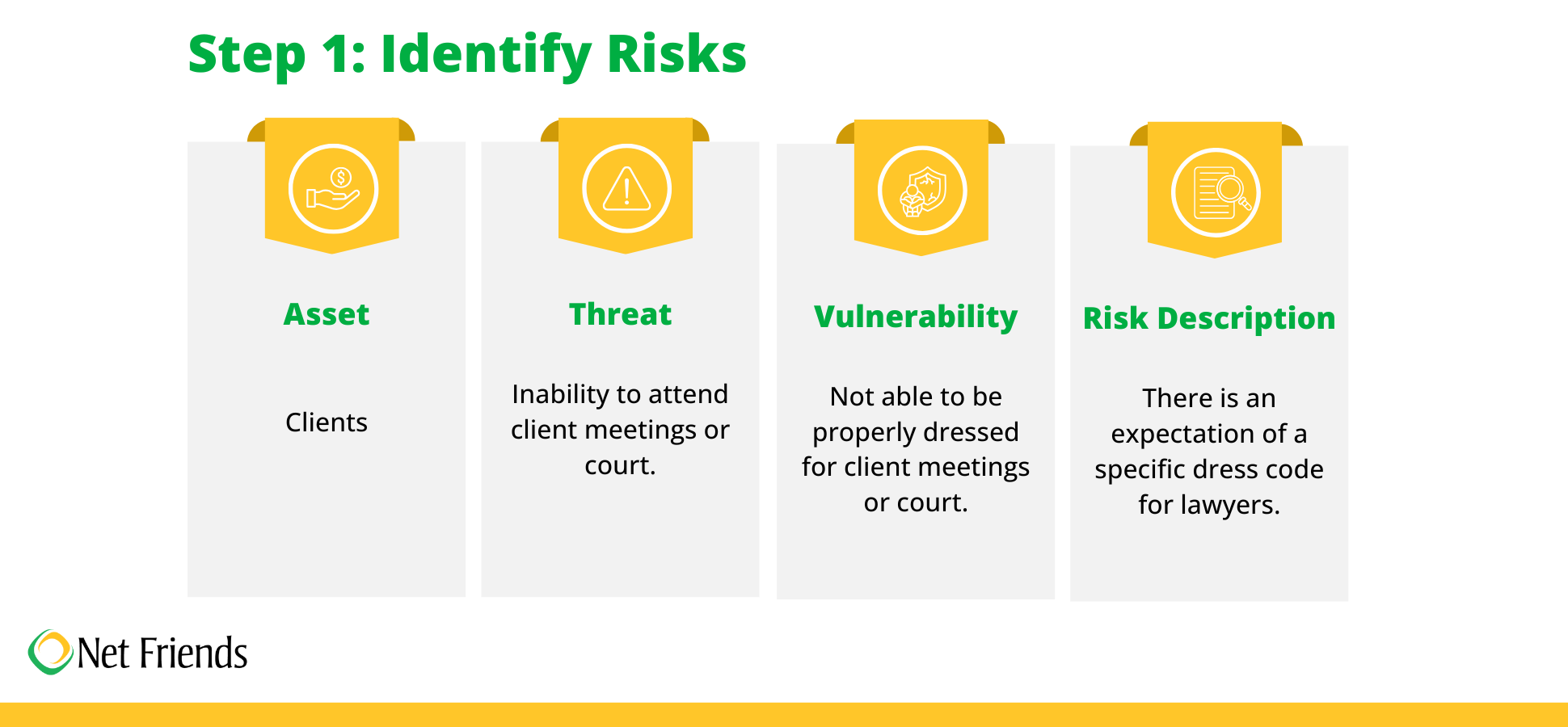
For this exercise, we will create a risk assessment spreadsheet, using my father's decision to save his "boring" suits. His risk fell under the Clients category.
Identify Risks
Identifying and categorizing risks is the next step. This process begins with systematically brainstorming potential threats, vulnerabilities, and hazards that could impact an organization, project, or process.
Once identified, these risks are then categorized based on shared characteristics, such as type of impact they could have (e.g., financial loss, reputational damage, safety hazards), or their likelihood of occurrence. This categorization helps to organize the risks, making it easier to analyze their potential impact and prioritize mitigation strategies.
For example, risks might be grouped into categories like natural disasters, technological failures, human error, or regulatory changes. A well-defined categorization system ensures that all potential risks are considered and provides a structured framework for subsequent risk analysis and response planning.
Building on my father’s decision to save his suits:
Evaluating and Prioritizing Risks
Once risks have been identified, the next step is to evaluate and prioritize them. This process involves analyzing each risk to understand its potential impact and the likelihood of it occurring. This allows for a systematic approach to focusing resources on the most critical threats.
Evaluating a risk involves considering two key factors:
- Likelihood (Probability): This refers to the chance or probability that the risk event will occur. Determining likelihood can be based on historical data, expert opinion, industry trends, or other relevant information. It is important to be realistic and avoid overly optimistic or pessimistic estimations.
- Impact (Consequence): This refers to the potential negative consequences if the risk event occurs. Impact can be assessed in various ways, depending on the context, including financial loss, reputational damage, operational disruption, legal liabilities, environmental impact, or harm to individuals.
By systematically evaluating and prioritizing risks, organizations can develop effective risk management strategies and allocate resources efficiently to mitigate the most critical threats. This process is iterative and should be revisited regularly as circumstances change and new risks emerge.
The risk of not being able to show up in court dressed properly was unlikely, but the impact of showing up in chinos and a t-shirt led my father to pack his closet in the trunk of his car.
.png)
Developing Risk Mitigation Strategies
Once risks have been identified and analyzed, now you can develop effective mitigation strategies. This involves determining the most appropriate response for each risk and outlining specific actions to reduce the likelihood and/or impact of the risk event. A well-defined mitigation plan is crucial for proactive risk management and minimizing potential disruptions.
For each identified risk, determine the most suitable response from the following options:
- Avoid: Taking actions to eliminate the risk altogether. This might involve changing plans, processes, or even ceasing certain activities.
- Accept: Acknowledging the risk and making a conscious decision to take no action. This is appropriate for low-impact risks or risks where mitigation costs outweigh the benefits.
- Share/Transfer: Shifting the risk to a third party, such as through insurance, hedging, or outsourcing. This doesn't eliminate the risk but transfers the financial or operational burden.
- Reduce: Implementing controls and actions to decrease the likelihood and/or impact of the risk. This is the most common response and focuses on proactive risk management.
As part of this process, you will need to establish a system for monitoring the progress of mitigation actions and tracking their effectiveness. This includes:
- Assigning responsibility: Clearly identify individuals or teams responsible for implementing and monitoring each action.
- Setting deadlines: Establish clear deadlines for completing actions and tracking progress.
- Regular reporting: Implement a process for regular reporting on the status of mitigation efforts.
- Updating risk assessments: Periodically review and update the risk assessment to reflect the impact of mitigation actions and identify any new or emerging risks.
By following these steps, organizations can develop comprehensive risk mitigation strategies that effectively reduce their exposure to potential threats and enhance their ability to achieve their objectives. Regular review and adaptation of these strategies are essential to maintain their effectiveness in a dynamic environment.

Review and Update
Effective risk management isn't a "set it and forget it" process. The business landscape is constantly evolving, introducing new threats and transforming existing ones. This is why conducting regular reviews is critical to maintaining a robust and adaptable risk management framework. These reviews should encompass:
- Monitoring: Tracking key risk indicators to identify trends and potential issues.
- Risk Assessments: Periodically assessing for new and emerging threats.
- Strategy Updates: Refining and updating mitigation strategies for continued effectiveness.
- Communication: Sharing risk information with all employees to foster awareness.
My father would call regular meetings to review and update our plans. As technology changed, we updated plans, for example when we all had cellphones we created a communication hub with a person outside the area. This is why it is beneficial to regularly review these plans and risks to make sure they still make sense.
A well-documented risk assessment not only enhances an organization's ability to protect its essential assets but also fosters a proactive and resilient approach to navigating an increasingly complex and uncertain world.
Not sure where to get started? Net Friends is here to help! You can book a meeting with one of our experts and we will be happy to lend a hand. Also, download our Risk Assessment Template!
Suggested Reading
How Security Assessments Help Businesses Conquer Cyber Threats
Transferring Risks with Managed Services and Cyber Insurance
Server Hardening 101: Boosting Business Security
Take IT Off Your To-Do List.
Tech holding you back? Losing productivity to downtime?
Discover how we can simplify your tech and free up your time, contact us today.
At Net Friends, we believe in the power of human expertise. While we leverage AI to enhance our content and processes, all blog posts are written and edited by our knowledgeable staff. You can trust you are getting insights directly from our team.

